RISK MANAGEMENT WITHIN SIX PHASES
WHAT IS INCIDENT RESPONSE PLAN AND WHY IS IT IMPORTANT?
Threats and danger can never have an ending and we can’t always avoid them. In prehistoric times, when man used to live in caves, he must have been avoiding the wild beast by lighting fire and hiding in the caves. But what happens if the threat comes in the form of snake, while he is expecting lion or a tiger. We can’t always prepare ourselves from every possible danger and at some point an unknown threat will manifest itself and can leave us injured or worse dead.
This happens the same way when cyber-criminals attack large organisations and leave them with very difficult situation to deal with. Cyber-attacks are planned for various reasons and it only meant to destroy the business internally. Internal threats have always proved to be the most dangerous and it is an effective strategy for cyber-criminals to plan. Within the network structure, a malicious actor gets installed through malicious means such as phishing, and it seek out the information it requires or to temporally blocked out the computer system while it do the job of destroying the internal network structure. For financial gain, degrading competition, terrorism and at times for amusement, breaches occur within the organisation. A cyber-attack like that destroys organisational reputation, its long developed dignity and exploits its assets to bring a halt to its growth and in some cases to permanently eradicate the organisation from the competition.
So, if the threat is unavoidable, that doesn’t mean we stop preparing ourselves from such attacks. Rather we need more secure plans and security to protect our organisation from even an unknown threat. So how do we do that? To answer this, let’s take an example of an office building where an accident happened in the kitchen that leads to spreading of fire on the entire floor. What will be the first rescue response? Someone might take a fire extinguisher and blow it to the fire or someone buzz the alarm alert that leads to activate the respond system of water sprinklers. What if both of these situations didn’t happen because of unavailability of the first two aids. The fire will keep on spreading until the whole building and the people in it are in tremendous danger. Then the fire fighters come on being called only in the worst of the situations, when it is no longer controllable. This is how our community arranges a hierarchy of risk management. Fire extinguishers and water sprinkles are installed in the building to prepare and to control the fire problem at first glance and if it gets way serious, then we have the number to dial to call the fire rescue team. In all the cases, we have aids to protect ourselves and our assets from all kinds of danger and early on preparation ensures less danger for the future.
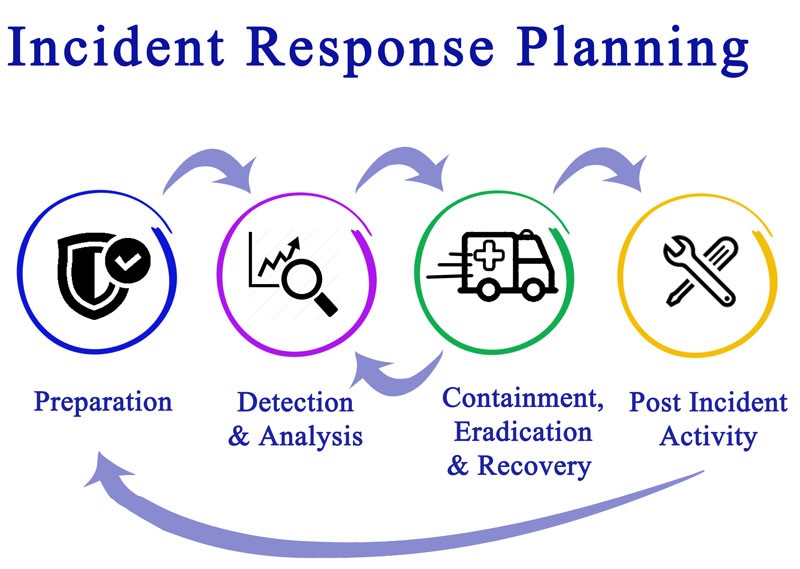
This is how, INCIDENT REPONSE PLAN works in organisations to rescue the firm from internal threats and cyber-attacks. It identifies the problem and then takes necessary measures of response to control the situation and to learn from past mistakes, so that it would know how to deal with the similar situation in the future.
An incident response plan is a tested, trained and well-documented technology that works to prevent data and monetary loss and to stop the normal operations in the event of a security breach. It is like a digital insurance that every organisation requires in order to make their business safe and secure from cyber-attacks. Therefore, it becomes more crucial for all kinds of businesses to take an incident response plan by outside parties, that partnership of digital insurance can diminish the risk of future breaches.
Ready to experience the full power of cloud technology?
Our cloud experts will speed up cloud deployment, and make your business more efficient.
HOW TO CHOOSE THE BEST INCIDENT RESPONSE PLAN FOR YOUR BUSINESS?
NIST (National Institute of Standards in Technology) offers multiple models on which any organisation can choose and use the best IRP model for their business. NIST, a professional body of institution that works in developing better IRP services, guides through their available resources to build a strong Incident response plan for your business, some models are as follows:
- CENTRAL: Within the central model of response, a central body of institution handles the response system against cyber-attack such as CSIRT (Computer Security Incident Response Team).
- DISTRIBUTED: In distributed model of response system, there are multiple response teams who are responsible to monitor on a specific location or affected area.
- COORDINATED: In coordinated model of response system, a specific body of institution is responsible for undertaking and conveying response plan to the affected organisations or businesses.
Once you have chosen the best suitable model for your organisation, then it becomes way more important to understand Incident Response Plan’s six phases:-
SIX PHASES THAT DETERMINE TO MAKE AN INCIDENT RESPONSE PLAN WORK
To create an incident response plan, make sure that you have addressed carefully and completely the following six phases of IRP:
- PREPARATION: Just like we got trained how to respond to fire incident or earthquakes, that kind of drilling and training ensures that more and more people and children will know how to deal with such situations, the more less likely that it will affect us in major way. Through training and preparation, we humans have learned that we can wear off any disaster and tackle it with skilled behaviour when an actual event occurs.
In the same way, a cyber-breach is no less than a natural disaster when it befalls on an organisation. A malware attack takes away all the data, either to destroy the business or to use it against. Therefore, planning is the key element to prepare ourselves to learn to tackle with those situations.
In the preparation phase of the incident response plan, keep the following points in mind:-
- Train your employees: Train your employees in a way that each one knows their roles and responsibilities when an actual breach occurs.
- Drill scenarios and mock data breaches: Within organisation, conduct drill scenarios where employees are trained on a regular basis on how to deal with a breach and a mock test will ensure their learning.
- Make sure the availability of all the necessary resources: Not having the updated software or hardware can result in a breach incident, so it becomes way more important to invest and make available all the resources in advance.
- Get approval in advance: From the main director of the organisation who is responsible for all the execution within the system, it is a must for the organisation to get the approval in advance for employees training fund.
Your response plan should be aiming at maintaining proper documentation and should be tested multiple times to ensure that the employees are ready to perform their key roles and responsibilities during an actual breach incident. The more the employees will get trained; they less likely that a breach will occur and it will also aid in maintaining the efficiency level of skills in handling a breach situation of the organisation as a whole.
- IDENTIFICATION: Identification is the phase where the computer system or experts identify through notifications or disturbances that a malicious actor has been installed within the network system. It alerts the user of its presence and entry point gateway, so that immediate measures will be taken.
- CONTAINMENT: The mistake that is often seen and done during an actual breach is that the user or the employee deletes that data that has been affected. By doing that, the only source of evidence get lost to detect the initial place where the malicious host got entered. Instead, you should contain the breach right there, so that it won’t get spread to damage the business. An organisation ought to have long term and short term strategies ready to deal with the situation. It’s good to have a backup data to help to restore business operations. That way no important information can get lost forever in oblivion.
This is good phase in time to update and patch the old systems, to strengthen the requiring authentication identification of each employee in the organisation, especially those who work remotely through systems of network. It is a good idea to change all the user credentials and passwords harder to guess.
- ERADICATION: Eradication is the time to patch up the damage that is made and secure the securities systems harder than ever. In this phase, a thorough analysis should takes place to find out the root cause of the breach and from where it is made. By root cause, we mean finding every inch of the network systems, finding out which applications have been affected and the last but not the least, what tools, tactics and procedures have been employed by the cyber-criminals for the breach.
During this analysis, organisations are supposed to fill out, patch the new vulnerabilities that they discovered during this stage and to get rid of the malware that is affecting the software from within. If any trace of a malware in the system remains, the user or the organisation will still be losing essential data which will eventually increase the liability of the business.
- RECOVERY: So many questions haunt us when a malicious attack occurs e.g., when can the business be returned to its normal pace? Are the new updated systems being properly patched? Is there another chance of a breach to occur? And so on. That’s why, you need an incident response plan, either you develop your own IRP, or hire a third party to do that for you. In any case, the business needs to return to its former form and restoring, recovering the data that has been lost. This is the phase where the process of restoring and returning the affected systems to its full-fledged form takes place and retaining the business to its previous environment without the fear of being hacked again.
- LESSONS LEARNED: After the investigation phase, the organisation should keep a meeting with all the incident response team, to discuss the lessons learned from such a breach. A proper RCA (Root Cause Analysis) Report should be prepared, wherein all the gathered metrics should be incorporated with updating of new policies and employee training, procedures, plans and tactics should tales place. A proper analysis between the drill training and the real cyber-attack incident should form a conclusion of the things where the spot has been missed and what worked and what doesn’t. A proper documentation of the lessons learned will ensure blocking of the similar attacks in the future, whether in the same organisation or the other.
As we started our discussion from prehistoric times, why not end it at the same point. We humans are extra-ordinary creatures, who have learned the importance of sharing and learning from other’s mistakes and vulnerabilities within our culture. In the cyber-community that shared culture is still applicable in 21st century and will continue to be. After a breach incident, the mistakes and learning are shared within our tech-culture, to save some other organisation from the same sort of threat. Remaining in a healthy competitive market will in fact strengthen us; therefore sharing the lessons learned from a cyber-attack incident is a way of helping each other from meeting the same fate that we are capable of preventing against.








